Installation
By default, the application usage agent is disabled in the standalone agent. To enable it during installation:
- Locate the [Usage Agent] section with the mgssetup.ini file.
- Remove the semi-colon (;) from the front of the following line:
;USAGEAGENT_DISABLE = False
Agent Configuration
The following table lists the managed device preferences that determine which types of applications are included in application usage metering:
|
Type of application |
Preference |
Default |
|
Add/Remove Program entries |
UseAddRemove |
False (not included) |
|
Manually mapped applications (see Specifying the list of applications to meter for further details) |
UseManualMapper |
False (not included) |
|
Applications run by a logged-in user |
UserProcessesOnly |
True (only applications executed by a logged-in user are included) |
|
Applications packed in the native package format (Windows Installer, RPM, or PKG) |
UseMSI |
False (not included) |
To see all configurations that can be made in terms of usage agent, refer to Chapter 9 of the “RayManagesoft Deployment Manager Discovery Guide.pdf”
Below is a watered down version of what needs to be done to get the Application Usage Agent working in an environment.
Note 1: If you find during testing that the amount of uploads has dramatically increased, then you can either increase the value for the Upload period in seconds option or set the Enable upload within usage agent option to false for production.
Note 2: If you find that any of the other options that have values in seconds to be too aggressive during testing, then make sure to change their values for production.
Manual Mappings
A manual mapping allows you to target applications that are either excluded by an agent option or if you do not wish the agent to target all applications, by creating registry entries under the following key:
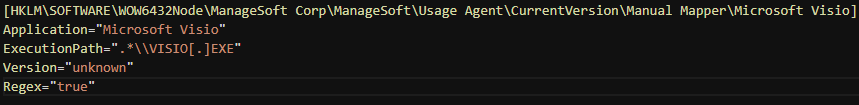
This is an example of how Microsoft Visio usage can be tracked. It is recommended to use regular expressions for the ExecutionPath, as you do not have to provide a full path that might differ between product versions.
Full details can be found in the aforementioned chapter in the Discovery Guide.
Note: If new mappings are added to the registry, then the 'Security Manager Service' service will need to be restarted as part of that action in order for the usage agent to include them in its process monitoring.
Application Usage by Application Report
Usage data is displayed for each application on a weekly basis:
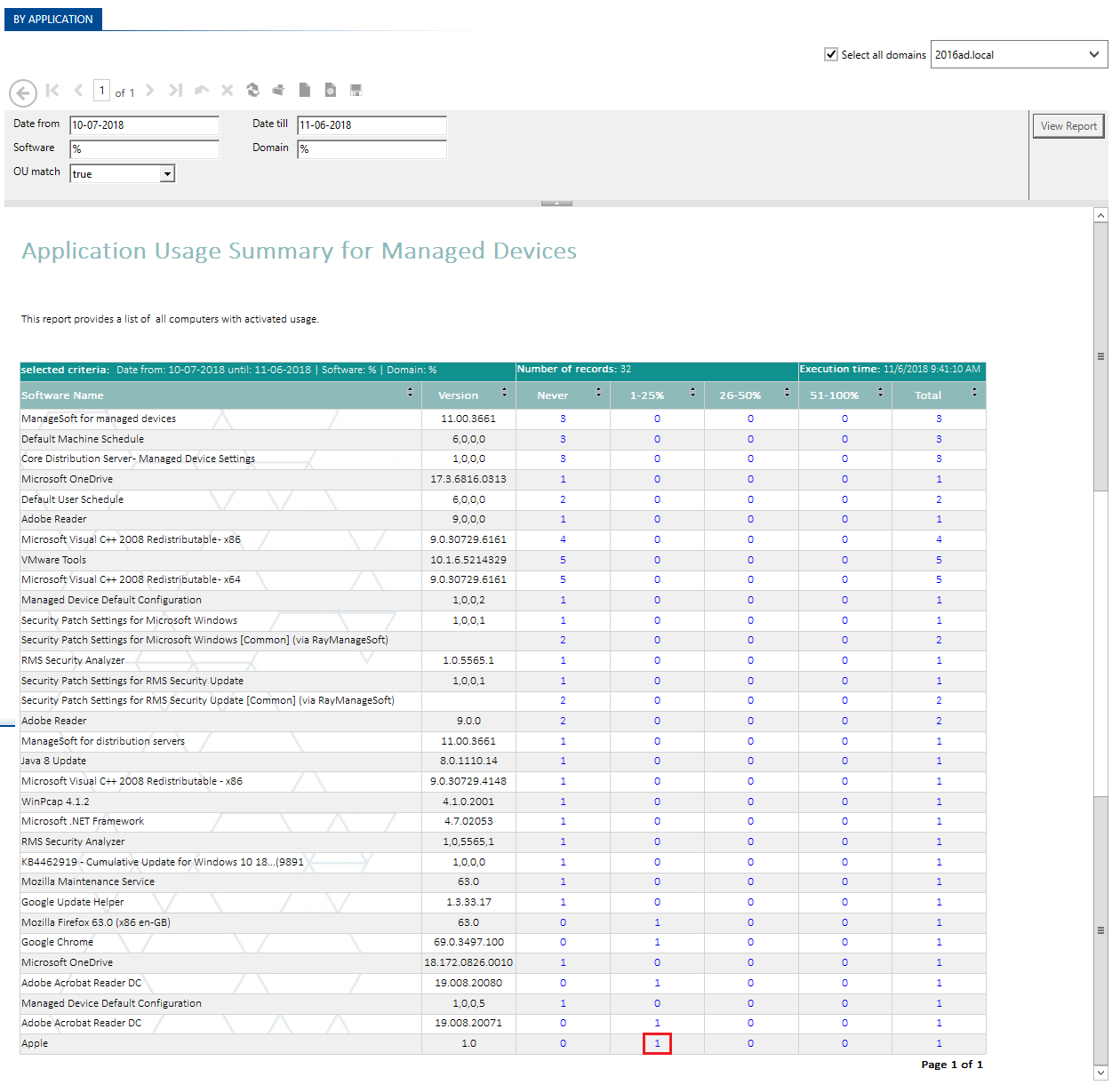
Drilling down displays the list of devices that the tracked application has been used on:
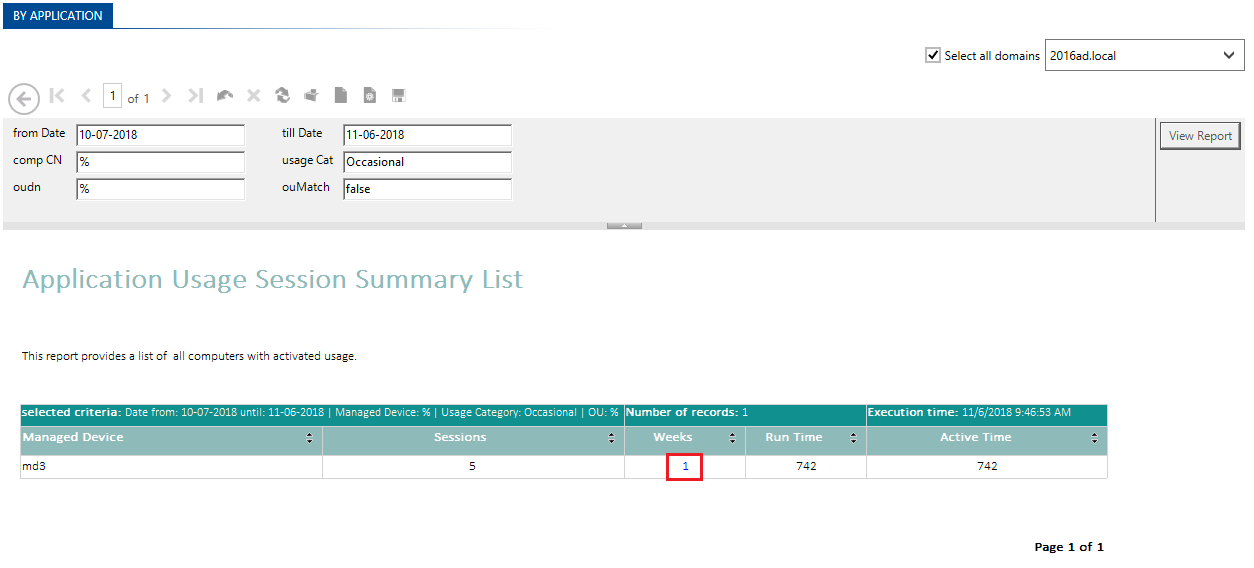
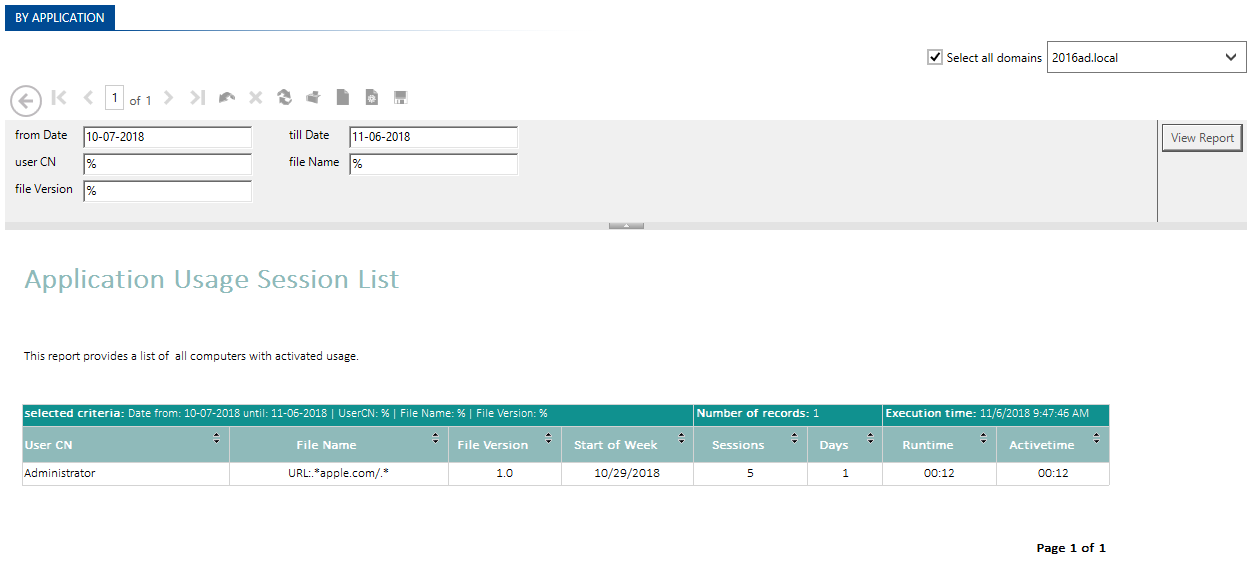
Drilling down further allows you to see the actual usage time on a specific device:
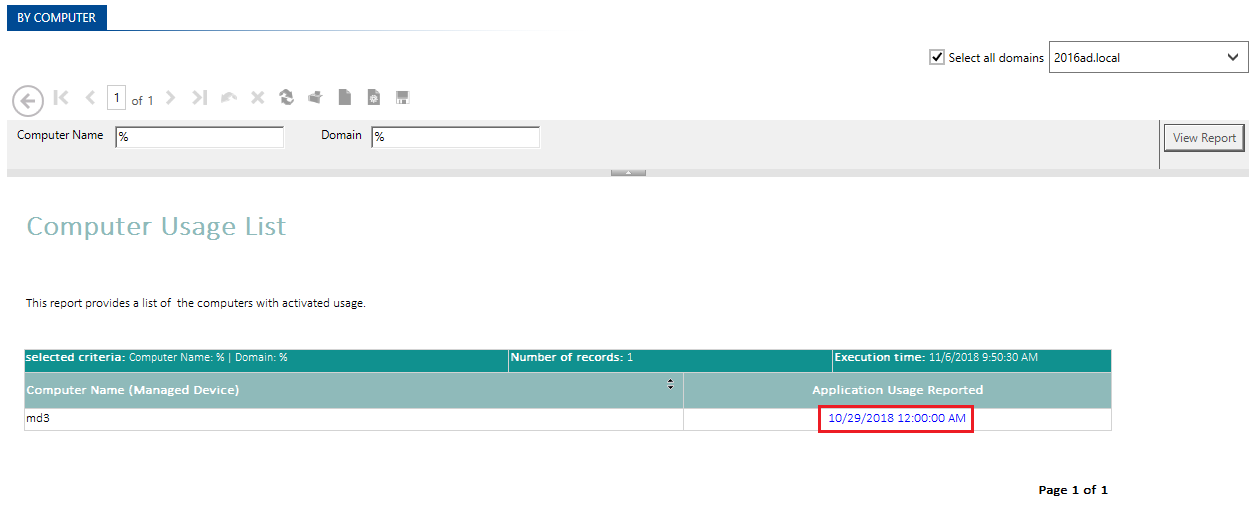
Application Usage by Computer report
This report displays a list of devices that have usage data associated with them:
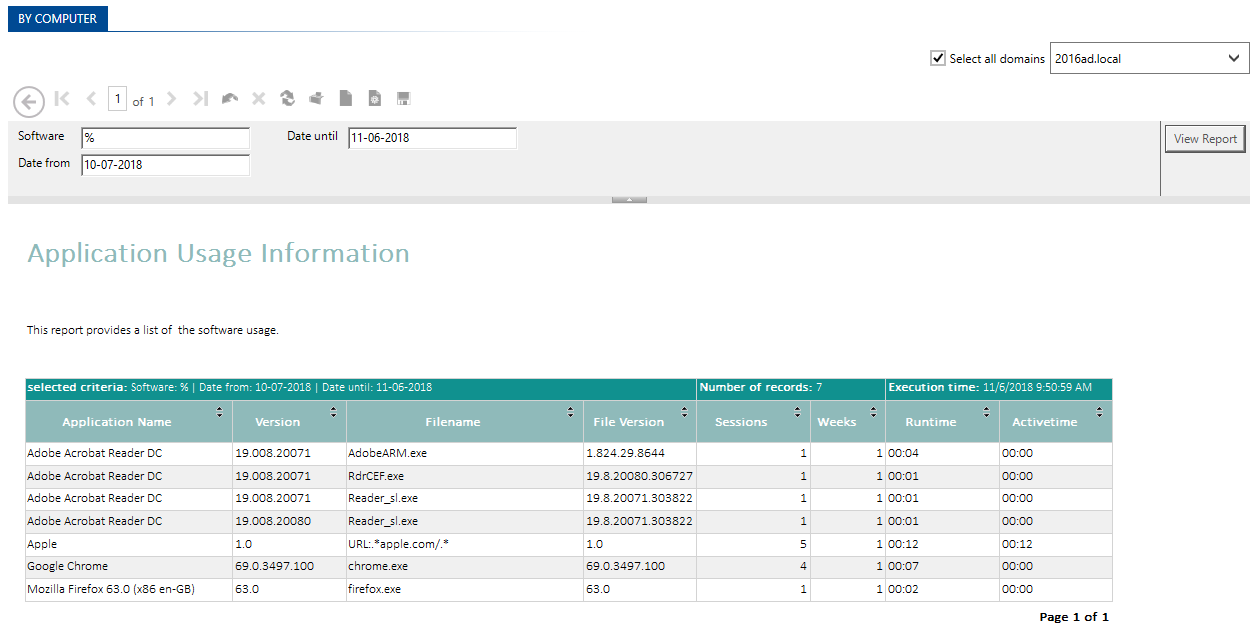
Drilling down lists all applications pertaining to that particular usage session:
Comments