This article describes the steps required to implement SSL within IIS, RMS's infrastructure framework, and for its managed devices.
IIS
Once an SSL certificate has been created (self-signed web hosting certificate, internal Certificate Authority certificate, or an external CA certificate) and imported into IIS, the following actions need to be taken:
- Add a HTTPS binding to the relevant web site:

- Select the SSL certificate that should be associated with this binding.
Note: Do not enter a host name value nor enable the 'Require Server Name Indication' option if a self-signed certificate will be used.
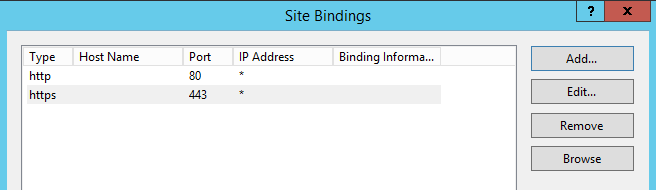
Note: The HTTP binding can remain because when IIS is configured to require SSL it will reject any HTTP calls.
- If all applications and virtual directories within the web site will use SSL, then configure the web site to require SSL:
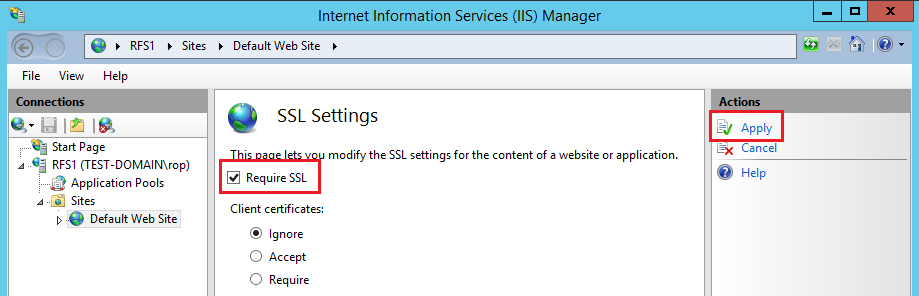
Note: If en existing environment is being changed to HTTPS, then this option should not be enabled until all DS's and managed devices have received new configurations that include the SSL entry points.
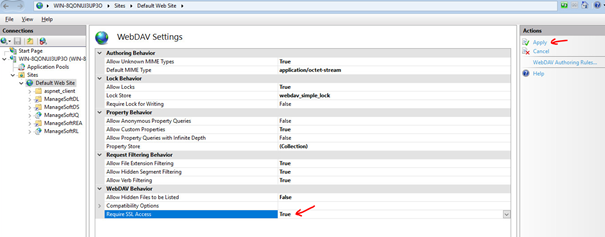
- If any application or virtual directory utilises WebDAV, then configure the web sites WebDAV feature to require SSL access:
Infrastructure
- Edit the relevant distribution server object within the OVERVIEW tab so that it uses HTTPS as its protocol as well as its required port.
- Edit the relevant distribution location object within the DISTRIBUTION tab so that it uses HTTPS as its protocol as well as its required port.
- Edit the relevant reporting location object within the REPORTING tab so that it uses HTTPS as its protocol as well as its required port.
- Perform a verify configuration action so that all DS's receive an updated 'hierarchy.cfg' file.
- Redistribute either the global failover package or the relevant group(s) failover package(s) so that managed devices will receive upüdated failover locations the next time they perform an update policy action.
Managed Device
- If an 'mgssetup.ini' file is used to install the managed device and a self-signed certificate will be used, then the following lines need to be added to this section:
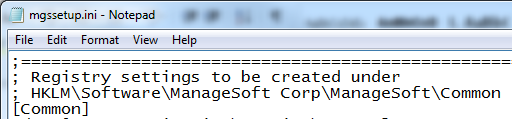
; If you use https with not signed certificates,
; it’s better to disable certificate checks
; for this remove ; in front by desc37-desc38 and val37-val38
desc37 = CheckCertificateRevocation
val37 = False
desc38 = CheckServerCertificate
val38 = False
Note: the descxx and valxx numbers should be changed to meet your specific INI entries.
- For existing managed devices, their managed device settings package(s) should be modified to include the following two options if a self-signed certifcate is being used:
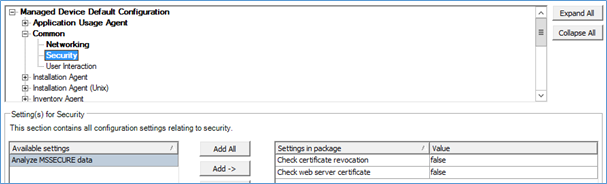
Note: Change the package version before re-distributing it.
Comments